Privacy on your terms
Giblex builds local-first security tools designed to keep sensitive systems closer to the user who owns them.
Instead of relying on cloud accounts, sync layers, and remote trust assumptions, Phantom products focus on local storage, device presence, and narrower access paths.
The goal is simple: systems that unlock only when the right conditions exist on the system you control.
Trusted device present and unlock conditions satisfied
Encrypted at rest and available offline
Private retrieval and memory workflows
Segmented restoration with controlled continuity
Security with fewer assumptions
Most software assumes remote infrastructure should sit in the middle of access, storage, or recovery. Giblex takes a narrower approach: keep sensitive workflows local wherever possible, and require physical device presence for access when it matters.
Keep sensitive workflows local
Sensitive data should remain on systems the user controls whenever possible, instead of depending on remote infrastructure by default.
Make possession part of access
Phantom Key is being built around split-key and device-presence checks so protected workflows can require something you physically control.
Independent tools, shared trust model
Each Phantom product solves a different problem, but they are designed to work together under the same local-first security model.
Different tools, one security model
Phantom products cover encrypted storage, authentication, verification, recovery, auditing, and device-bound access. Each product has a specific role, but they share the same core idea: sensitive systems should rely on fewer external dependencies and clearer access conditions.
Phantom Attestor
Phantom Recovery
Phantom Examiner
Phantom Key
Giblex Assistant
A vault that stays local and opens only when it should.
Phantom Obscura stores credentials, files, notes, and sensitive records in a local encrypted vault. Access can be tied to a trusted USB device, adding a physical requirement to digital security.
📅 Launching May 2026
Your data stays on your system, and access can depend on a device you physically control.
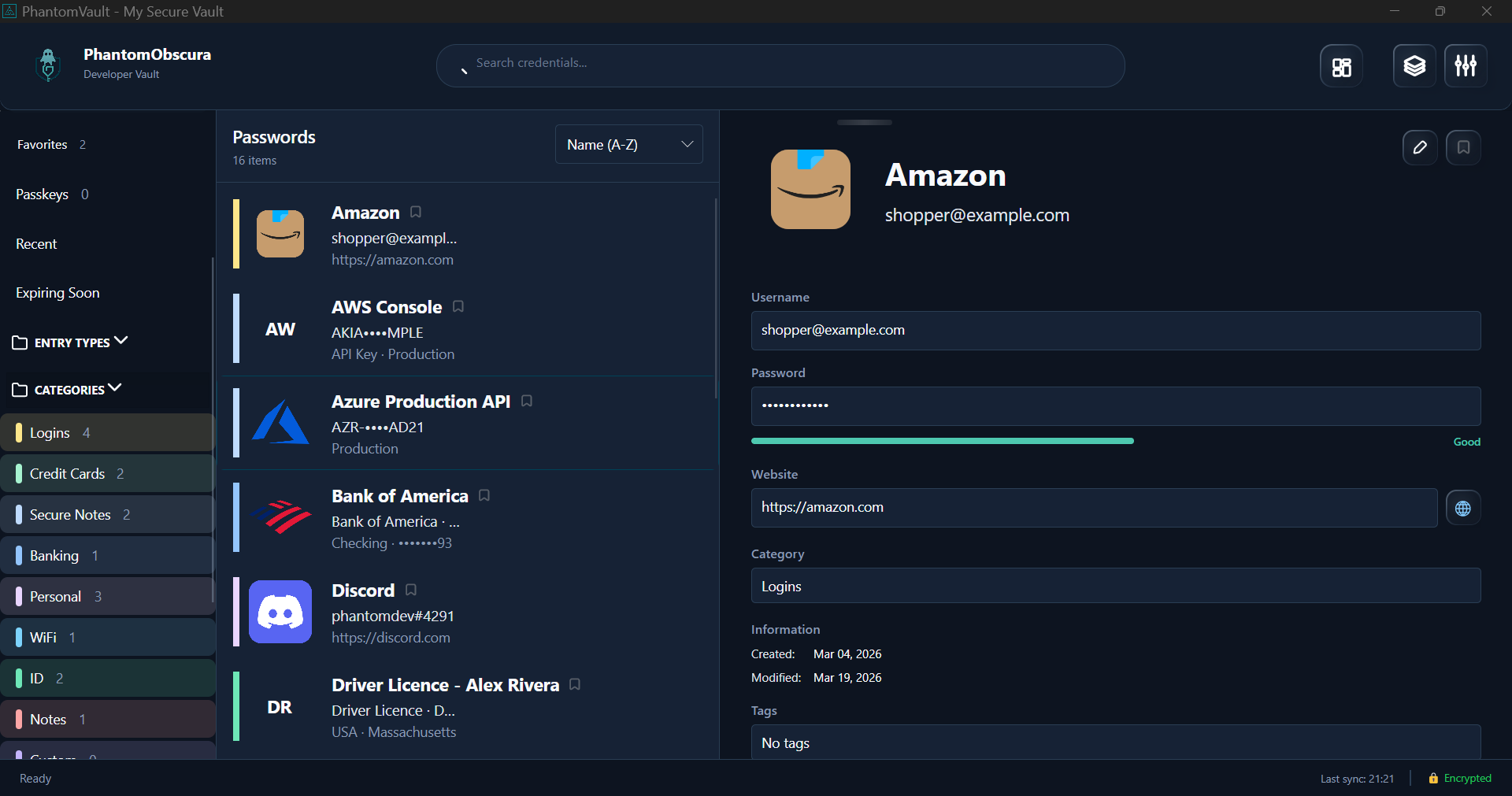
Layered controls, applied locally
Sensitive data should remain on systems users control whenever possible.
Remote infrastructure should not sit at the center of every sensitive workflow.
Trusted device presence can become part of the access path instead of an afterthought.
Security decisions should be understandable so users can see what access depends on.
Each product works on its own, but they are designed to fit together cleanly.
Security pages that explain the model
A plain-language explanation of the assumptions behind local storage, device presence, and controlled recovery.
A technical view of the layers involved in root trust, vault containers, session control, and integrity enforcement.
A realistic summary of what Phantom products are designed to protect against and what remains out of scope.
Join the Phantom waitlist
Phantom products are currently under development. Join the waitlist to follow progress and receive updates on early access releases.